ReportServer 4.3.0 Features
Script datasinks
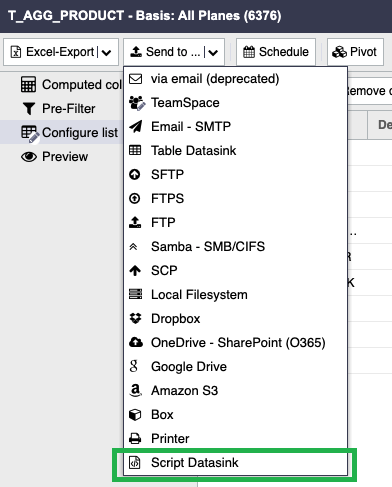
Script datasinks are your swiss army knife when it comes to sending your reports/your data to custom locations or when you need any logic or any additional files. Basically, you can use script datasinks to send your reports/your data to virtually any location you may need. Refer to the following screenshots.
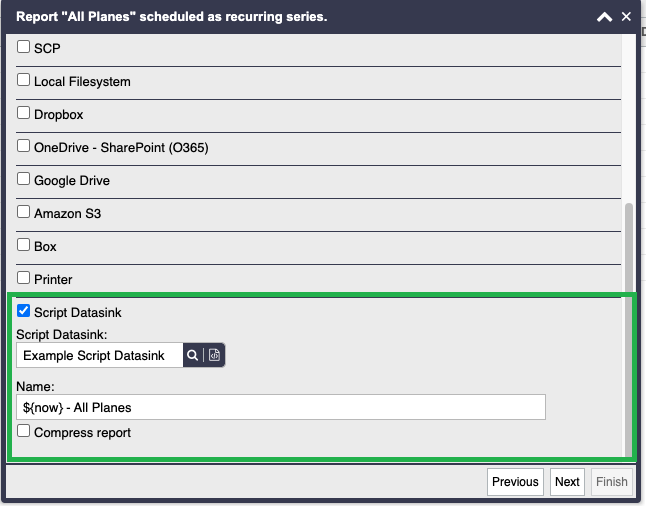
An example script datasink is shown below. It creates a ZIP containing the report/the data, adds the groovy script to the ZIP and sends this per email to a given user list.
package net.datenwerke.rs.samples.tools.email
import net.datenwerke.rs.core.service.mail.MailBuilderFactory
import net.datenwerke.rs.core.service.mail.MailService
import net.datenwerke.security.service.usermanager.UserManagerService
import net.datenwerke.rs.utils.misc.MimeUtils
import net.datenwerke.rs.core.service.mail.SimpleAttachment
import java.nio.file.Paths
import java.time.LocalDateTime
/**
* scriptDatasinkPerEmail.groovy
* Version: 1.0.2
* Type: Script datasink
* Last tested with: ReportServer 4.3.0
* Sends a given report/given files per email
* and includes the script groovy file in the ZIP.
*/
def mailBuilder = GLOBALS.getInstance(MailBuilderFactory)
def mailService = GLOBALS.getInstance(MailService)
def userService = GLOBALS.getInstance(UserManagerService)
def mimeUtils = GLOBALS.getInstance(MimeUtils)
// the user ids. They have to exist and the ids are passed as long (L)
def to = [123L]
def subject = 'Script datasink'
def content = "ReportServer script datasink ${LocalDateTime.now()}"
// name of the zip
def attachmentFilename = 'data.zip'
def attachments = [
new SimpleAttachment(data, // you can also use report
mimeUtils.getMimeTypeByExtension(datasinkConfiguration.filename),
datasinkConfiguration.filename),
// add the script
new SimpleAttachment(script.data, script.contentType, script.name)
]
def mail = mailBuilder.create(
subject,
content,
to.collect{userId -> userService.getNodeById(userId)})
.withAttachments(attachments)
.withZippedAttachments(attachmentFilename)
.build()
mailService.sendMail mail
Test LDAP GUID configuration via “ldaptest guid” terminal command
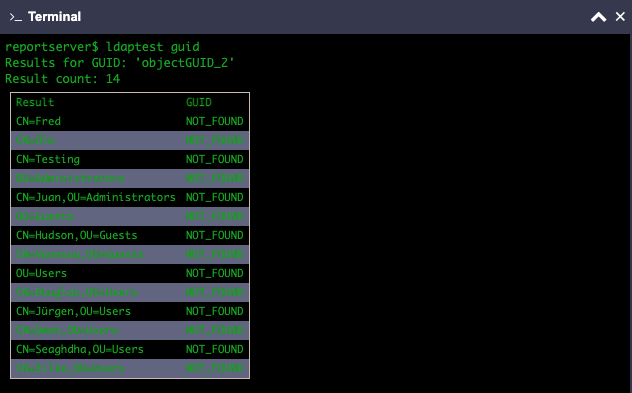
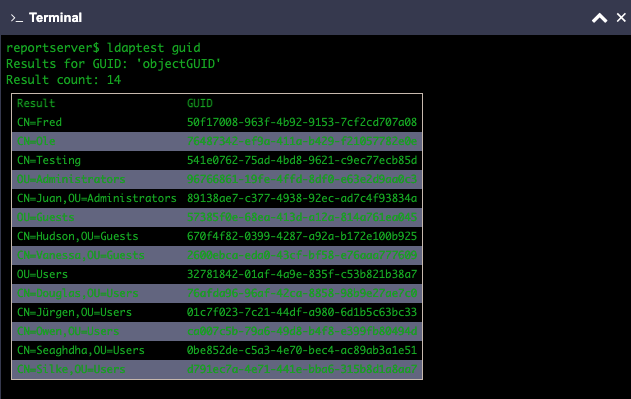
You can now test your LDAP GUID configuration as shown in the following screenshots. This helps troubleshooting LDAP problems/incorrect configuration together with the the other ldaptest commands described here.
The first screenshot shows an incorrect GUID configuration, as “objectGUID_2” does not exist.
After correcting the property to “objectGUID”, the correct GUIDs are shown in the next screenshot.
Integrate LDAP authentication
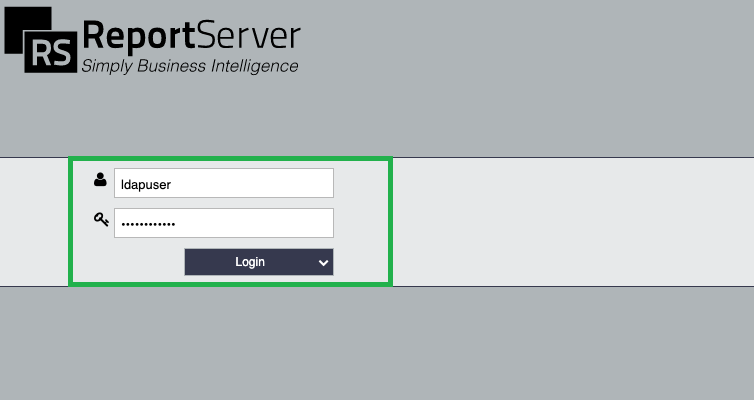
As of ReportServer 4.3.0, LDAP authentication is supported out-of-the-box. For using it, you have to install the net.datenwerke.rs.ldap.service.ldap.pam.LdapPAM or net.datenwerke. rs.ldap.service.ldap.pam.LdapPAMAuthoritative PAM in your reportserver.properties configuration file as described here.
Further, the ldap.cf configuration file was adapted in order to configure if local users are allowed to authenticate alongside with LDAP users:
<authentication> <allowLocalUsers>true</allowLocalUsers> </authentication>
The complete ldap.cf configuration file is shown below.
<?xml version="1.0" encoding="UTF-8"?>
<!--
ReportServer Configuration File
filename: sso/ldap.cf
Configures LDAP
-->
<configuration>
<provider>
<host>directory.example.com</host>
<port>389</port>
</provider>
<security>
<!--
Allowed values are: none/starttls/ssl
Recommended is starttls.
-->
<encryption>none</encryption>
<principal>CN=ldaptest,CN=Users,DC=directory,DC=example,DC=com</principal>
<credentials>password</credentials>
</security>
<base>OU=EXAMPLE,DC=directory,DC=example,DC=com</base>
<filter>(|(objectClass=organizationalUnit)(objectClass=user)(objectClass=group))</filter>
<externalDir>/usermanager/external</externalDir>
<writeProtection>true</writeProtection>
<includeNamespace>false</includeNamespace>
<logResultingTree>false</logResultingTree>
<flattenTree>false</flattenTree>
<attributes>
<objectClass>objectClass</objectClass>
<guid>entryUUID</guid>
<organizationalUnit>
<objectClass>organizationalUnit</objectClass>
<name>name</name>
</organizationalUnit>
<group>
<objectClass>group</objectClass>
<name>name</name>
<member>member</member>
</group>
<user>
<objectClass>inetOrgPerson</objectClass>
<firstname>givenName</firstname>
<lastname>sn</lastname>
<username>sAMAccountName</username>
<mail>mail</mail>
</user>
<additional>
<!--
You can request additional attributes including them here as:
<attribute>myAttribute1</attribute>
<attribute>myAttribute2</attribute>
-->
</additional>
</attributes>
<authentication>
<allowLocalUsers>true</allowLocalUsers>
</authentication>
</configuration>
